For many entrepreneurs, cybercrime is something that they don’t see happening to them. Maybe you too, don’t see the point of having an expert optimising your company’s security. It is worth it! We illustrate our tip with the true story of a small SME that not only lost a lot of money due to a cyber-attack, but also suffered severe damage to its reputation with customers and suppliers.
Ransom for files: a common demand
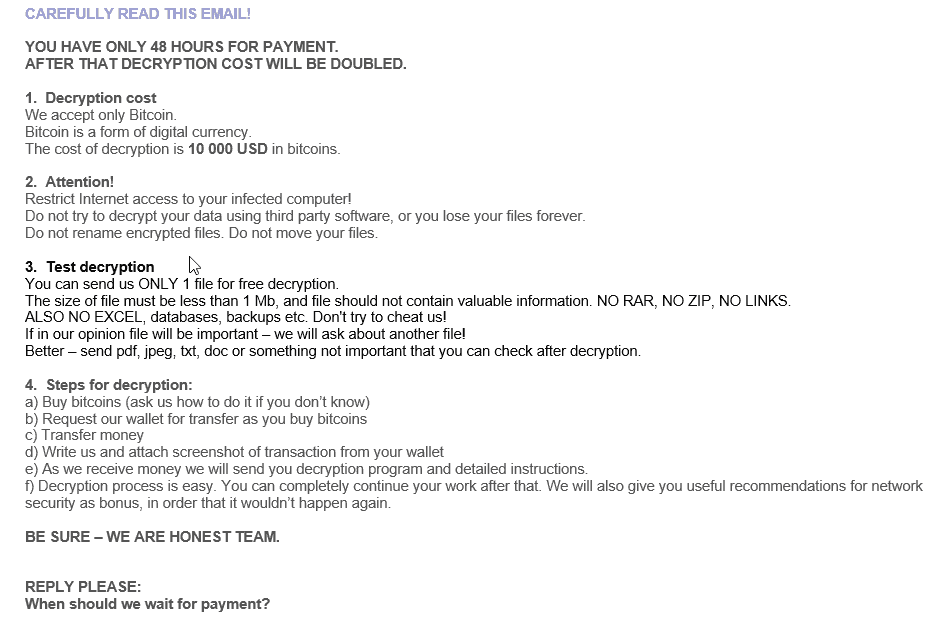
Cybercriminals had gotten hold of files from the SME and made it clear what demands the company had to meet to get them back:
“You have only 48 hours for payment, after that decryption cost will be doubled.”
This is usually the first line in an email from cybercriminals after you contact them to get your files released. Sounds ominous? It was. Check out this day-by-day report.
Day 1: The damage is done
On a Monday morning, the employees of the SME want to get to work, but nobody manages to log into the IT system.
Encrypted files
After a call to the IT partner’s helpdesk, the SME discovers that it’s been the victim of a cyber-attack and that all the files on the server have been encrypted with so-called ransomware. The only readable file is a text document stating that the SME has been hacked and should contact a specific email address if they want the files back.
Backup restoration attempt
Initially, the IT partner tries to restore a backup, so that the SME can return to the situation before the attack. The partner estimates that this could easily take a day. This means at least one day without income and three employees technically unemployed for those hours.
By noon, however, it’s becoming clear that a large number of backups are encrypted, making them unusable. The attack appears to have started as early as Friday evening, which also makes the weekend backups worthless. What to do now? After some recriminations – the business manager blames the IT partner for a lack of measures against this type of attack, while the IT partner blames the business manager for not having allocated a budget and for not having taken external security seriously – the IT partner finally turns to Netcure.
Contacting the criminals
We advise the SME to file a complaint. We assist the business manager in preparing a file for the police and collect the necessary data. From now on, all further steps are also documented and added to the file.
After a quick analysis, the only solution appears to be to contact the criminals to get the files back. It is important to release as little information as possible that can identify you (the victim). So it is better not to use your trusted email system. General services such as Gmail and Outlook are usually not enough to shield you completely either.
Netcure makes the first contact; the waiting game then begins. The SME has lost a full day and has no access to its history. In other words, it cannot access its invoicing data, accounting, stock lists, warehouse management or email. And there are many more consequences:
the SME must inform all calling customers that the systems are inaccessible and that the team is technically unemployed
the SME cannot process deliveries
it is not possible to deliver to customers either, because no one can see the outstanding orders.
The transport company the SME works with for deliveries has to adjust its planning and charges extra for this.
Day 2: Reply from the hackers
After about 15 hours – which leads us to suspect that the criminals are in a different time zone – we get an answer. The cybercriminals ask to send two encrypted files. From these files, they can identify the process by which this attack happened and even possibly determine the location of the target.
Day 3: The problems continue
It takes another 20 hours before we receive the text shown above. The ransom is set at USD 10,000.
Three days later, the SME is still unable to help anyone or follow up on outstanding orders. Customers are already becoming less understanding, and some of them are looking for an alternative supplier. Other customers are beginning to wonder whether their data have been revealed to the criminals and whether data has been leaked or stolen. Parties such as the transport company also have little sympathy for the sudden loss of income.
Day 4: Ransom negotiations
The costs begin to rise and the business manager is willing to pay a ransom, but does not have the USD 10,000 immediately available. Nobody is willing to step in, and the SME gets nasty questions about its (future) creditworthiness.
In the meantime, we are trying to negotiate the ransom amount down. The criminals are not prepared to do this as they don’t care if a small business in Belgium goes bust.
Day 7: Decision time
One week on and the situation is unchanged. Until, after days of negotiation, an agreement is finally reached. We manage to get the ransom amount down significantly, and the SME wants to proceed with payment. It still has to cough up a large sum and has no guarantee that the files will be available again after payment. However, there is no alternative.
Day 10: Processing the payment
The payment process takes another three days. On the tenth day, the amount is transferred to the criminals’ Bitcoin account.
Day 11: Access, at last
On day 11, the SME finally gets a tool that makes the files available again. All’s well that ends well, right? Unfortunately, no.
The conclusion: enormous damage
The SME really suffered from the cyber-attack.
At least seven working days with complete loss of income, technical unemployment of the workers and a huge backlog of work due to complete inactivity.
Serious damage to the reputation , both with customers and suppliers.
Affected creditworthiness with suppliers and financial institutions.
Breakdown of trust between the SME and its IT partner.
Cost of the ransom.
Costs for consultancy assistance during the negotiation process.
How the SME could have avoided this
This story sounds quite dramatic, and it becomes even more so when you know that it really should not have come to this. In this particular case, the disaster could have been avoided by correctly configuring the firewall and regularly analysing the protection measures. The means to stop a cyber-attack were available, but were simply not applied in the best possible way.
What would a similar scenario mean for your business? Make no mistake: even if you decide to pay immediately, it will always take at least a couple of days before the situation is rectified. Fortunately, a few simple measures can seriously reduce the risk of a cyber-attack. Let an expert assist you to better arm your business against cybercrime.
Trust us, we’re crazy about cybersecurity!